E-invoice login: access management and minimum security requirements
Other
E-invoice login — access management and minimum security requirements | Syneo
E-invoice login security fundamentals — RBAC, MFA, SSO, logging, and API account management for finance and IT to create an auditable baseline.
digitalization, e-invoicing, access management, MFA, SSO, RBAC, integration, API, logging, information security, compliance, IT consulting
March 6, 2026
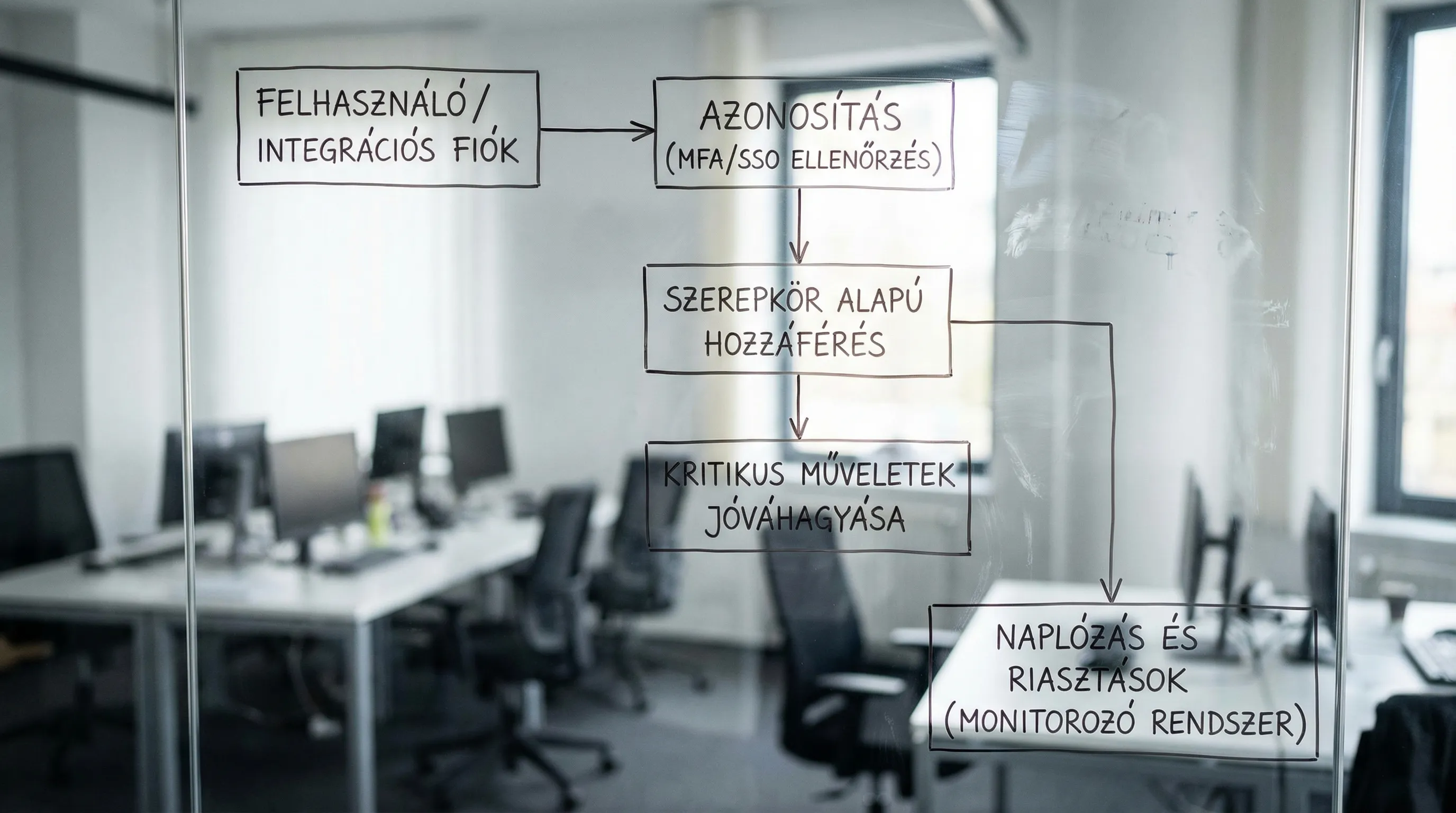
With the spread of e-invoicing (and the rise of standard, machine-readable formats between 2025 and 2028), e-invoice entry is no longer "just" a user experience issue, but a financial, compliance, and information security risk point. A compromised account not only has access to invoice data, but typically also to partner databases, bank account information, approval processes, exports, API keys, and in many cases ERP integrations.
In this article, I summarize the fundamentals of access management and minimum security requirements related to access, so that finance and IT can translate them into internal rules, settings, and auditable evidence.
Why is the introduction of the e-invoicing system a particularly sensitive issue?
E-invoicing systems are both financial systems and document management interfaces:
From a financial perspective, they have a transactional impact (issuance, cancellation, partner data, statuses).
Documents often contain personal data (GDPR), trade secrets, contractual data, and performance information.
From an integration perspective, APIs, technical users, webhooks, and ERP/CRM connections appear, which can function as "invisible entry points."
The attack surface is therefore typically not a single password, but a combination of identification + authorization + workflow + logging.
Access management principles for e-invoicing (where most errors occur)
1) "Least privilege" and roles (RBAC)
The basic principle is simple: everyone should only have access to what they need for their work. In practice, this works best when organized into roles (RBAC), especially in SME and mid-market environments.
The following sample is not product-dependent, but rather a "common-sense minimum":
Role | Typical task | Critical prohibitions (good practice) |
Invoicing (issuing) | invoice issuance, customer selection | cannot manage global settings or users |
Approver | approval, return, limit management | not be able to approve their own invoices |
Accountant / Financial Administrator | export, container data, report | do not be a system administrator (separation) |
System Admin | technical settings, integrations, permissions | do not perform business approval |
Auditor / read-only | view log, report, document | no modifications, exports may also be restricted |
Integration account (service account) | API calls, data connection | interactive access denied, minimal scope |
The most common "quick but dangerous" solution is a shared account ("accountant@...") or a shared password. This cannot be audited and cannot be traced back in the event of an incident.
2) Segregation of duties (SoD)
In financial processes, a recurring control is the separation of duties: whoever creates something should not approve it, and whoever is an administrator should not also be a business approver.
This is not bureaucracy, but fraud and error prevention, especially when exports are recorded in the system, bank transfers are prepared, or invoicing is automated.
3) Every login should be linked to an identity
If an external accountant, temporary substitute, or project-based financial actor works in the system, they should also have a unique identity (and time-limited authorization).
The NIST SP 800-63B guidance provides widely referenced fundamentals on digital identity and authentication best practices (e.g., modern approaches to authentication factors and password management).
Minimum security requirements for e-invoice access (don't go live without them)
Most of the controls below are "boring basics," yet this is where most implementations fail. The goal is not to overdesign everything at once, but to have an auditable minimum baseline.
Control area | Minimum requirement | What evidence can you show? |
MFA (multi-factor authentication) | mandatory for all interactive users | screenshot of settings, policy export |
SSO (if available) | central identity management, blocking in one place | IdP policy, access logs |
RBAC | roles documented, permissions reviewed | role matrix, quarterly review minutes |
Password and authentication policy | modern principles, prohibited passwords, brute force protection | policy settings, lockout rules |
Session management | inactivity timeout, secure cookie setting | configuration, security test report |
Managing admin accounts | separate admin, minimum number, "break-glass" control | admin list, traces of access requests |
Joiner/Mover/Leaver process | Admission, transfer, and discharge with SLA | ticket, HR-IT process description |
Logging and audit trail | access, authorization, export, deletion logged | log patterns, SIEM rules |
Control of exports | mass export restriction, watermark, approval (if necessary) | settings, DLP rules |
Integration accounts / API | service account, scope limit, key rotation | vault setting, rotation protocol |
Encryption | TLS, data storage protection on the provider side | service provider security doc, contractual annex |
Backup and archiving | access protected, reset tested | restore test report |
MFA: not an "option," but a fundamental requirement
If the e-invoicing system does not support MFA, this already poses a supplier risk. If it does support it, the question is: how do you enforce it and how do you handle exceptions (e.g., a break-glass account that is strictly controlled and logged).
The OWASP Authentication Cheat Sheet is a good starting point for authentication and access patterns, as it clearly lists typical attacks and defensive measures.
Session and login: shorten, connect to device, log
The e-invoice interface often runs from a browser. For this reason, session settings (cookies, timeouts, re-authentication for sensitive operations) are not "developer details" but financial controls.
For session management, the OWASP Session Management Cheat Sheet provides practical minimums.
Admin users: keep them few and separate
A typical anti-pattern: the financial manager is the "admin for everything" because it's faster. However, in the event of an incident, this is precisely what makes it impossible to limit the damage.
Minimum recommendation:
Admin role only for those who configure and integrate.
Business approval and admin should not be the same person.
Have a documented, rarely used break-glass account (stored in a safe with access logged).
Entry life cycle: joiner, mover, leaver in finance
In practice, access management is not determined at the "login screen," but rather by changes.
Joiner (admission)
When granting access, the minimum requirement is that there is a record of the authorization request (ticket, email approval, workflow) and that it is clear who can grant which roles.
Mover (role change, substitution)
When replacing someone (due to vacation or illness), the best practice is to use up the remaining entitlement. Remember: "we'll take it back later" rarely happens in reality.
Leaver (termination)
The most important factors here are speed and centralized blocking. If you have SSO/IdP, blocking should be done there, because this way it will take effect in all related systems in addition to the e-invoicing system.
Integrations and technical access: API accounts are also "users"
In e-invoicing, it is common for ERP, document management, or accounting automation systems to communicate via API. This is convenient, but it is one of the most risky aspects in terms of security.
Minimum requirements for integration access:
Service account without interactive login: if possible, do not allow login via UI.
Scope limit: only allow the API operations you need (for example, only queries or only account synchronization).
Confidentiality (secrets): keys should not be stored in code, but in a vault, with rotation.
Rotation and suspension: there should be a process for key replacement and immediate revocation in the event of an incident.
If you want a broader view of integrations, it is worth reviewing the auditable approach to connecting ERP, CRM, and BI (for example, event-driven or iPaaS patterns), because authorization and logging are key issues there as well.
Logging and auditing: what do you need to be able to retrieve in 5 minutes?
In e-invoicing systems, it is not enough to simply have a log somewhere. The goal is to be able to respond quickly to disputes or incidents:
Who logged in, when, and how (was MFA successful)?
Which user created, modified, or canceled which invoice?
Who exported data (especially bulk exports)?
Who changed the permissions or system settings?
Which integration key ran, with what calls, and with what errors?
If you have SIEM or central log collection, e-invoice login events and admin changes should be marked as "high severity" because these are the best early indicators.
Supplier risk and legal aspects: access is also an issue in the contract
In the case of SaaS e-invoicing, some of the minimum security requirements are the responsibility of the service provider (data protection and access controls, incident management, log retention). Therefore, it is worth specifying the following in the procurement and contract:
what authentication options are available (MFA, SSO),
what logs are available and for how long,
how long it takes the service provider to respond to an incident,
how data export and exit occur.
Interestingly, the same mindset applies to other "valuable" digital assets, such as IP, brands, content, and licenses. If you have exposure in these areas, a specialized approach such as Third Chair (monitoring, enforcement, licensing) can be a good example, where access and auditability become business value.
Quick, practical implementation plan (basics can be sorted out in 2 weeks)
The schedule below is intentionally simple because the goal is baseline, not perfect enterprise IAM.
Time slot | Focus | Output |
Days 1–2 | role models, SoD, identification of critical operations | role matrix v0, prohibited combinations |
Days 3–5 | MFA enforcement, admin account cleanup | MFA policy, admin list, break-glass rule |
Days 6–8 | joiner/mover/leaver process and approval | brief process description, responsible parties, SLA |
Days 9–11 | logging, export controls, alerts | log source list, 3–5 alarm rule |
Days 12–14 | integration accounts and confidentiality | service account inventory, rotation plan |
When is it worth bringing in an outside team?
For most organizations, securing access to e-invoicing becomes difficult when multiple systems are involved (ERP, accounting automation, SSO, permissions, auditing, backup) and cannot be managed with a single setting.
In such cases, it is worth seeking external support, for example:
role matrix and SoD planning,
SSO and identity management implementation,
auditing integration accounts and API accesses,
logging and incident process development.
Syneo can typically help with this by conducting assessments and providing implementation support: the goal is to establish a working baseline that supports both fast financial processing and auditable IT security requirements.