Cybersecurity for SMEs: 10 minimum controls by 2026
Other
Cybersecurity for SMEs: 10 minimum controls by 2026 | Syneo
10 auditable baseline controls for SMEs by 2026: MFA, backup, patch management, EDR, logging, and incident response — practical steps for rapid risk reduction.
cybersecurity, SME, MFA, EDR, free, patch management, incident management, NIS2, logging, IT consulting
February 28, 2026
By 2026, cybersecurity will no longer be an "IT issue" for SMEs, but a matter of business continuity. Data theft is increasingly supported by AI, and ransomware not only encrypts data, but also leaks it and then blackmails victims by threatening to make it public. Meanwhile, supply chain requirements are also becoming more stringent (audit questionnaires, insurance conditions, NIS2 impact through partners).
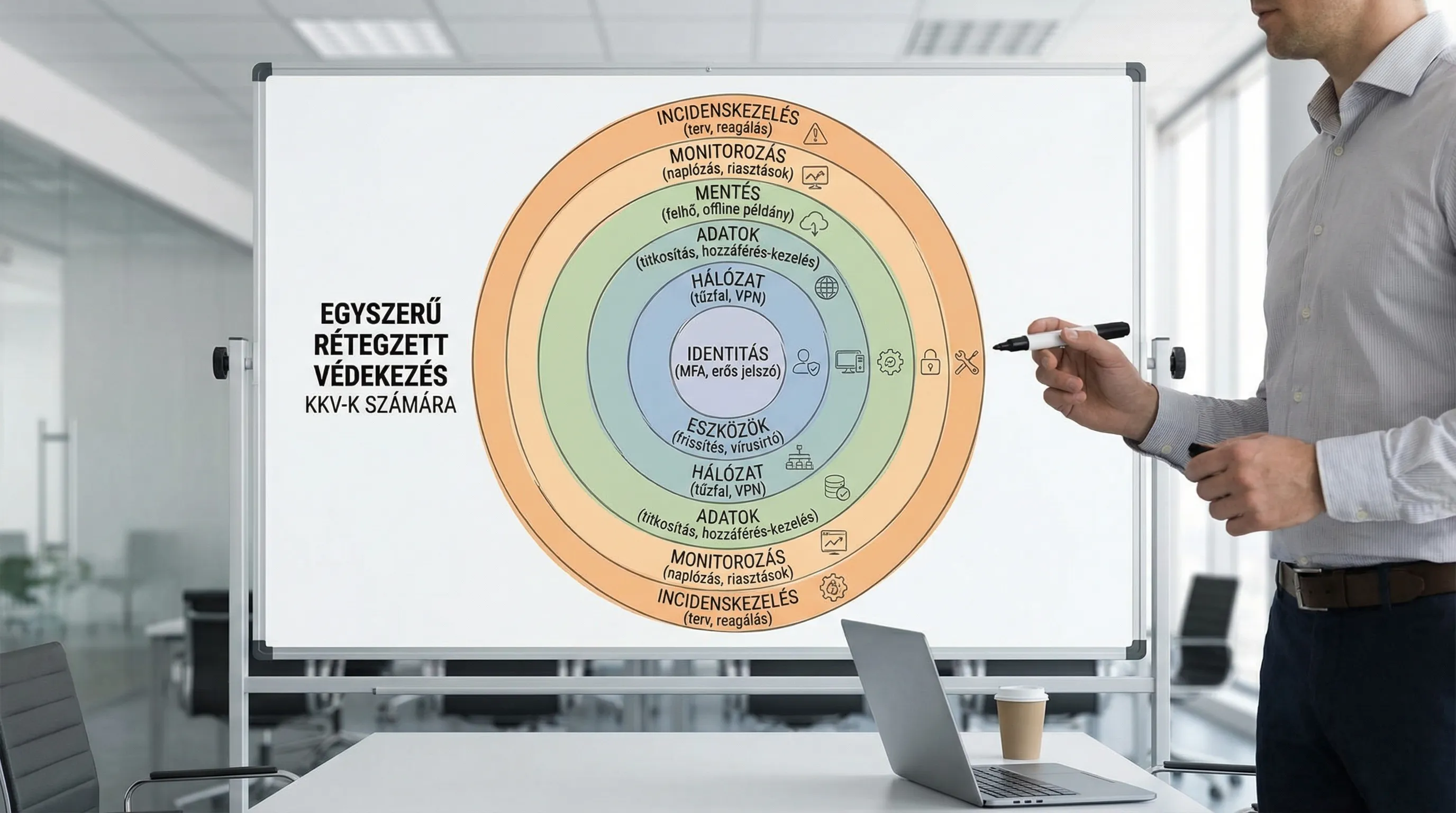
The good news is that for most SMEs, the majority of risks can be significantly reduced by implementing 10 basic controls, often without purchasing new equipment, through consistent settings and responsibilities.
What does "minimum control" mean here?
In this article, "minimum control" refers to a verifiable (auditable) security solution that:
blocks the most common attack vectors (email, password, endpoint, lack of updates),
reduces the impact of an incident (rescue, separation, rapid response),
and does not only exist on paper (there is an owner, a measurement index, and a monitoring schedule).
The NIST Cybersecurity Framework 2.0 and the CISA's practical target system (CPG) are good reference points as frameworks for SMEs as well, because they are business-oriented and focus on the "what should I do tomorrow" level.
How to use this list (SME-friendly)
Don't try to do everything at once. The goal is to establish a stable baseline, after which you can build more sophisticated controls (SIEM, DLP, Zero Trust, etc.).
Recommended operating principle:
Every control should have an owner (name, not "IT").
Every control must be supported by evidence (screenshot, report, ticket, policy, log).
Have a rhythm (weekly, monthly, quarterly checks).
10 minimum controls by 2026 (for SMEs)
1) Equipment and inventory list (know what you have)
If there is no inventory, there is no control. Attackers love "forgotten" laptops, old admin accounts, and unmanaged SaaS subscriptions.
Minimum requirements:
All laptops/PCs/servers must be registered (owner, role, OS version, encryption status).
Every cloud application should have a list of accounts and a list of administrators.
Offboarding should be mandatory for departing colleagues.
Evidence: export from MDM/address book (Microsoft Entra ID, Google Workspace) and an up-to-date inventory table.
2) Mandatory MFA everywhere (especially: email, VPN, admin)
Compromising email accounts is now the most common entry point for account fraud and ransomware preparation.
Minimum requirements:
MFA is mandatory: email, file sharing, VPN, CRM/ERP admin interfaces.
Stronger protection for admin accounts (separate admin account, preferably a phishing-resistant solution, where available).
Disable old protocols where relevant (e.g., basic auth-type access).
Evidence: MFA enforcement settings, report on non-compliant users.
3) Password and access hygiene (least privilege, RBAC)
The "everyone sees everything" approach is convenient, but expensive in the event of an incident.
Minimum requirements:
Role-based access control (RBAC) in key systems.
Admin rights only in justified cases, limited in time, where possible.
Elimination of shared accounts (or at least replacement with personal accounts and logging).
Evidence: authorization matrix (who does what and why), quarterly review report.
4) Patch management and vulnerability management (not ad hoc updates)
Unpatched systems remain a top risk. In 2026, attackers will be able to "productize" newly published vulnerabilities faster than SMEs can patch them.
Minimum requirements:
Operating system and browser updates automatically, with supervision.
SLA for critical fixes (e.g., within 14 days, faster for Internet-facing systems).
Monthly report: what is behind schedule and why.
Evidence: patch compliance report, change log.
5) Endpoint protection (EDR or at least modern AV) and device encryption
Ransomware doesn't just attack servers. The "zero step" is often a laptop.
Minimum requirements:
Managed endpoint protection on machines (with alerts, not just installed).
Disk encryption on laptops.
USB and macro control where commercially justified.
Evidence: EDR console screenshot/report, encryption status report.
6) Email protection and anti-phishing routine
SMEs are often targeted by account number changes, fake supplier emails, CEO fraud, and password theft.
Minimum requirements:
SPF/DKIM/DMARC settings for the domain (at least monitoring, then enforcement).
Filtering risky attachments and links.
A simple, enforceable internal rule: bank account number changes can only be verified through two channels.
Evidence: DMARC status, email security policy, monthly phishing report, or training log.
7) Backup strategy based on the 3-2-1-1-0 principle (and recovery test)
Backing up isn't just about having a copy "somewhere." It's about being able to restore it.
Minimum requirements:
3 copies, 2 different media, 1 offsite, 1 immutable or offline, 0 restore failures (tested).
Backup for critical SaaS data (e.g., cloud files, email, CRM export, or backup solution).
Quarterly rollback test (at least 1 system).
Evidence: backup report, restore test report (date, RTO/RPO experience).
8) Basic network protection: separation, remote access control
In many SMEs, the "everything on one network" principle means that a single compromised machine can quickly spread laterally.
Minimum requirements:
Guest Wi-Fi on a separate network.
Separation of servers and admin interfaces, access control.
Remote access only in a managed manner (MFA, logging), closing unnecessary ports.
Evidence: network diagram (a simple one is sufficient), firewall rule list, and change log.
9) Secure operation of public services (hardening, DDoS, updates)
If you have a web app, customer portal, API, or VPN accessible from the internet, hosting and operational fundamentals are direct risk factors.
Minimum requirements:
Regular updates and configuration hardening.
DDoS protection and basic monitoring.
Separate admin access, key-based entry, logging.
If you are building on VPS and stable access is important, it is worth choosing a provider that includes anti-DDoS and managed support as part of the package. For example, this is a particular focus in the case of VPS hosting offered with anti-DDoS protection.
Evidence: hardening checklist, patch report, uptime, and alert settings.
10) Logging, basic monitoring, and incident management plan (practice instead of paperwork)
It is common for SMEs to experience "something happening," but it is unclear what happened, when it happened, and how it affected them. The goal is not to have a large corporate SOC, but to have a trail and a routine.
Minimum requirements:
Retention of critical system logs (e.g., 30-90 days), especially: email, identity management, VPN, servers.
Alerts for basic events: suspicious logins, mass file deletion, admin rights changes.
Simple incident playbook: who decides, who we notify, what to do in the first 60 minutes.
Evidence: list of alert rules, incident log (even if run on a test table).
Quick summary table (what to review before an audit questionnaire)
Control | Typical owner | Minimum evidence | Frequency of checks |
Equipment and account inventory | IT + HR | Inventory export + offboarding checklist | Monthly, immediately upon leaving |
MFA | IT | MFA enforcement report | Monthly |
RBAC / least privilege | System administrator + system owner | Authorization matrix, review report | Quarterly |
Patch management | IT | Patch compliance report | Monthly |
Endpoint protection + encryption | IT | EDR/AV report + encryption status | Monthly |
Email protection + process | IT + Finance | DMARC status + "account number change" rule | Quarterly |
Save + restore test | IT | Backup report + restore test | Monthly backup, quarterly testing |
Network separation | IT | Network diagram + firewall rules | Semester |
Hardening of public services | IT/DevOps | Hardening checklist + patch log | Monthly |
Logging + incident plan | IT + management | Alert list + playbook | Quarterly practice |
Typical pitfalls to avoid in 2026
"MFA is in place, done." Meanwhile, admin accounts are exceptions, or old access methods remain open.
There is a backup, but the backup resides in the same permission domain as the encrypted data.
Endpoint protection is installed, but there is no alert manager and no response.
Supplier access rights remain "forever."
If, while introducing controls, you realize that processes and responsibilities are lacking, it is worth starting with a short, business-focused assessment. The Syneo team can also help with IT consulting and implementation support (survey, prioritized roadmap, control setup, operational rhythm). The DevSecOps practical guide may also be useful if your company has development and CI/CD.
Frequently Asked Questions (FAQ)
Which of the 10 controls is the most important if I can only implement one? For most SMEs, mandatory MFA on email and admin access provides the fastest risk reduction, but without backup and recovery testing, you remain vulnerable to ransomware.
How long does it take to implement these 10 minimum controls in an SME with 30-100 employees? If there is a dedicated person in charge and the systems are not completely disparate, the baseline can be established in 4-8 weeks. If there are many exceptions, old systems, and no inventory, 2-3 months is more realistic.
Do you need expensive SIEM or SOC services for this? Not necessarily. At a minimum, it is more important to have logging, basic alerts, and an incident playbook. SIEM/SOC pays for itself quickly if you have a lot of public interfaces, a lot of endpoints, or compliance requirements.
What do larger customers typically ask of their suppliers? Most often, they ask for MFA, backup and incident management processes, patch management, access management, and evidence (policy, reports, audit logs). Often, it is not perfection that they want, but controlled operation.
How do I know that my backup is "ransomware-proof"? You are in good shape if you have an offsite copy, immutable or offline elements, the backup is not accessed by the same permissions as daily files, and you regularly test the restoration.
Next step: turn it into a 30-day baseline project
If you want to not only "check off" these 10 controls, but also operate them in an auditable manner, it is worth starting with a brief assessment of the situation: inventory, risks, quick wins, followed by a prioritized implementation plan.
Syneo's digital and IT consulting team will assist you in conducting the assessment, setting up controls, and establishing a stable operating rhythm. To get started, list your current systems (email, file sharing, ERP/CRM, VPN, servers, cloud) and consult with us about the next steps at syneo.hu.

