DevSecOps in practice: how to build secure CI/CD
Other
DevSecOps in practice: how to build secure CI/CD | Syneo
A practical guide to DevSecOps: how to build automated, risk-based, and developer-friendly CI/CD — secrets management, SAST/SCA, artifact signing, and SBOM.
DevSecOps, CI/CD, secrets management, SAST, SCA, SBOM, artifact signing, IaC, pipeline, security
February 19, 2026
CI/CD is no longer just about fast delivery, but also about ensuring that the pipeline is not the weakest link. A poorly protected build environment, a leaked token, or a compromised dependency can lead to a business incident just as much as a classic application vulnerability. The goal of DevSecOps is to make security not a separate phase at the end, but an automated, measurable, and developer-friendly part of the delivery process.
If you approach it from the DevOps side, it is worth looking at the big picture, and Syneo's previous material provides a good basis for this: DevOps basics: the path from zero to a live environment in 2026.
What does DevSecOps mean in practice (and what does it not mean)?
DevSecOps = DevOps + built-in security controls + shared responsibility. In practice, this typically means three things:
Security checks (at least some of them) run automatically in the pipeline, and problems are not only revealed during manual audits.
Controls are risk-based (we don't block everything, but we do block critical items).
There is feedback and accountability: who fixes it, with what SLA, how we measure it.
What DevSecOps is not:
Blocking all PR due to dozens of "red" tools that no one understands and ultimately turns off.
Introduction of a single SAST tool, while omitting secrets management, permissions, artifact release, and runtime monitoring.
Threat model for CI/CD: what are you actually protecting against?
You can build secure CI/CD if you clarify where attackers can interfere with the delivery chain. Typical risk points:
Source code and pull request process (poor branch protection, missing reviews, overly broad merge permissions).
Dependencies and package managers (compromised packages, typosquatting, vulnerable versions).
Build environment (persistent runner, too many permissions, "see-all" tokens).
Artifact handling (no signature, no integrity, untraceable, what went live).
IaC and deployment (incorrect security group, public bucket, overly broad cloud IAM).
Secrets ( key left in repo, token too widely accessible as CI variable).
The table below provides a useful "layered" approach to where controls should be built in.
CI/CD layer | Typical attack surface | Minimum DevSecOps control |
Code (repo) | bad review, dangerous change | branch protection, mandatory review, CODEOWNERS |
Dependency | fragile or counterfeit package | SCA, lockfile, version pinning |
Build | runner compromise, token theft | isolated runner, least privilege, OIDC |
Artifact | exchange, manipulation | signature, immutable registry, provenance |
Deploy | incorrect configuration, IAM too broad | policy-as-code, IaC scan, approval gate |
Runtime | unknown drift, attack | monitoring, logs, alerts, patch process |
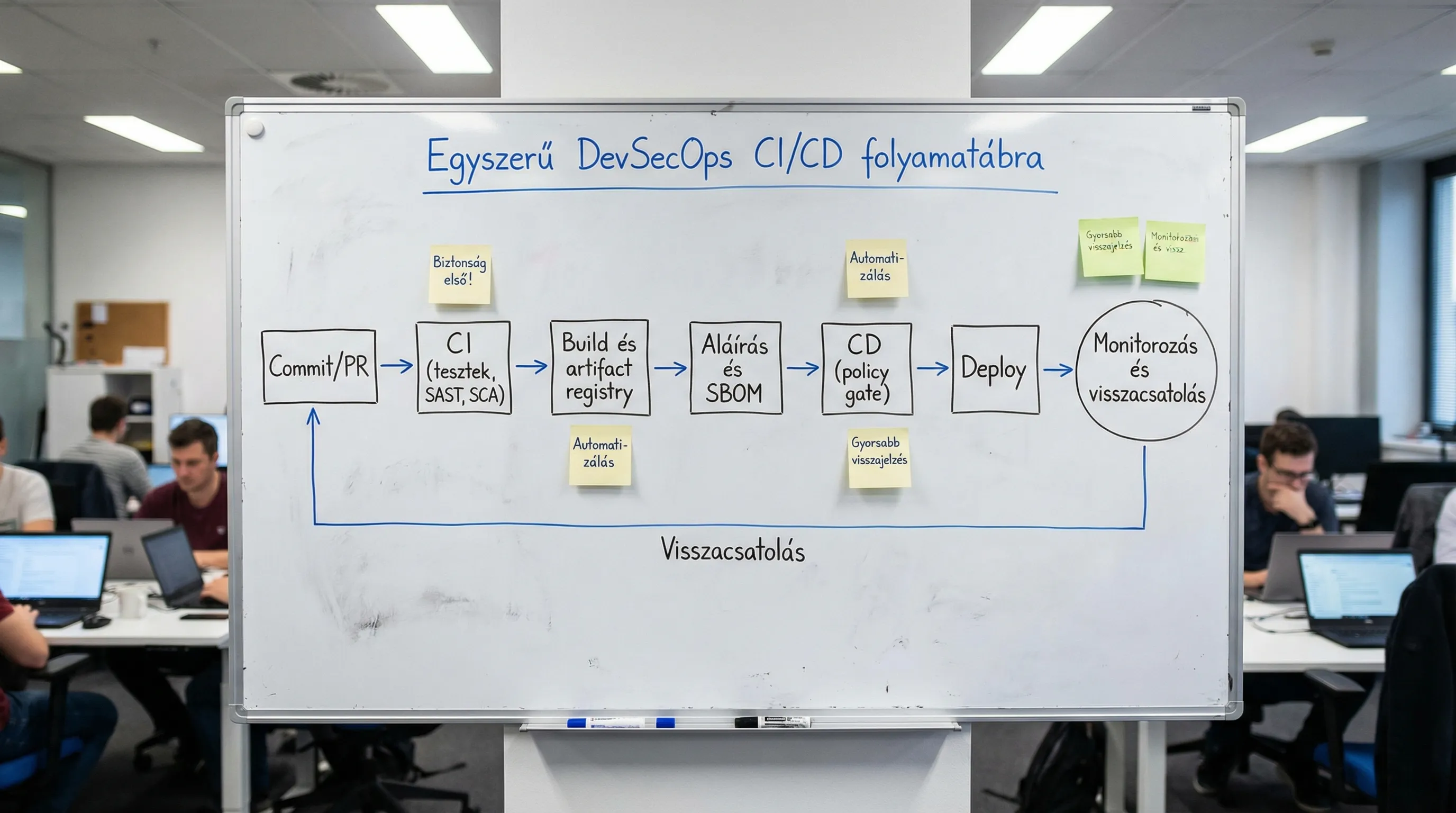
Reference architecture for a secure CI/CD pipeline
Most organizations operate a "basic" pattern that can be implemented independently of the platform (GitHub Actions, GitLab CI, Azure DevOps, Jenkins):
Pre-commit and PR level: fast, developer-friendly checks.
CI level: build, tests, code, and dependency checks.
Release level: artifact production, signature, SBOM, release records.
CD level: environment-specific policies, controlled rollout.
Runtime: monitoring, incident management, feedback to the backlog.
1) Pre-commit and PR: the cheapest mistakes should be found here
The goal is for the developer to receive notification of typical problems before merging. In practice, this could be:
Secrets scan (e.g., API key samples) to prevent keys from ending up in the repository.
Lint and basic static checks to ensure quality consistency.
PR rules: mandatory reviewer, "admin override" prohibited for critical repositories.
Tip: Speed is critical for PR-level controls. What you run here should take around 1-3 minutes, otherwise the team will "skip" it.
2) CI checks: SAST, SCA, IaC scan, container scan
The classic DevSecOps "four" in most modern stacks:
SAST (static code analysis): typical vulnerable patterns, dangerous function calls.
SCA (dependency analysis): known vulnerabilities, license risks.
IaC scan (Terraform, Helm, Kubernetes YAML): cloud and cluster misconfigs.
Container image scan: Vulnerabilities in OS packages and runtime dependencies.
The OWASP recommendations and initiatives related to the software supply chain (such as SLSA) are worth knowing as a source and a good starting point.
3) Release: artifact signature, SBOM, and "what went live?"
Many organizations fail because the pipeline runs out, but later it is impossible to say clearly:
which commit,
in which build environment,
which dependency versions,
exactly what was published.
This is where two key concepts come into play:
Artifact signing: confirms the integrity and origin of the artifact.
SBOM (Software Bill of Materials): a "parts list" for software that supports vulnerability management and auditing.
The goal is not to do everything "enterprise-style" starting tomorrow, but to have a minimally auditable release process. This is especially important in regulated industries and organizations affected by NIS2.
4) CD and activation: policy gate, environment segmentation, controlled rollout
A "secure CD" generally consists of three pillars:
Policy-as-code: environment-specific rules (e.g., no public storage, mandatory encryption, minimum TLS).
Environment-specific permissions: CI should not have admin access to production.
Controlled rollout: canary, blue-green, rapid rollback (if supported by the system and the business).
A common anti-pattern here is that the pipeline knows everything with a single service principal: dev, staging, prod. This is convenient, but expensive in the event of an incident.
Confidentiality (secrets): the most common real-life incidents
One of the fastest ways to get a return on DevSecOps is through secrets management discipline. Here are some best practices:
Do not store secrets in repositories, not even in "private" repositories.
Don't give long-lived tokens to CI if it can be avoided.
Use short-lived permissions and centralized secrets management (e.g., vault-type solution).
Audit who and what can read CI variables (fork PRs, job scope, environment scope).
In modern cloud environments, OIDC-based federated access (logging in with pipeline identity) is a good practice because it reduces the number of static keys.
Permissions and build isolation: "least privilege" in the pipeline too
The pipeline is often a "mini admin" in the system. That's why it's so important in DevSecOps:
Preference for ephemeral runners (disposable build machines) over persistent runners.
Tokens with minimal scope (repo read, artifact write, nothing else).
Separate CI identities for each project, not a common "company-ci-admin."
Network restrictions, for example, the build should only access what it needs (artifact registry, dependency mirror).
This is not just security, but stability as well: there is less chance that a pipeline will "accidentally" overwrite something in production.
When should the pipeline block, and when should it just signal? (risk-based gating)
If you try to block everything, the team will eventually disable the controls. If you block nothing, DevSecOps becomes a mere decoration. In practice, a simple policy works:
Hit type | Example | Recommended pipeline behavior |
Critical, exploitable | public RCE, key added to repo | blocking, immediate repair |
High risk | Severe CVE in Internet-facing component | blocking before release, fixed SLA |
Medium | vulnerability of non-internet-facing components | does not block PR, but ticket and SLA |
Low | best practice deviation | report, backlog, trend measurement |
The bottom line: write down (even if it's just one page) what you consider to be a "stop ship" category.
Secure CI/CD as a compliance tool (audit evidence)
For many companies, DevSecOps is not only a technical issue, but also a compliance issue: "Can we prove that we deliver in a controlled manner?" The following are useful for this:
Pipeline log retention (who deployed what and when).
Release notes and artifact identifier (version, digest).
SBOM storage linked to release.
Manage approvals (if necessary), but within an automated framework.
If you take measurability seriously at the project level, Syneo's previous article on goals and risks provides related insights: Planning a digitalization project: goals, KPIs, risks.
30-day implementation plan (realistic, not a "big bang")
When introducing DevSecOps, the best tactic is to take a gradual approach. Here is a typical 30-day plan that is easy to understand:
Period | Focus | Tangible results |
Days 1-7 | baseline and quick wins | branch protection, secrets scan, minimal permissions |
Days 8-14 | CI controls | SAST or SCA implementation, initial rules for blocking |
Days 15-21 | release discipline | artifact storage organization, versioning, basic SBOM |
Days 22-30 | CD and policy | environment segmentation, IaC scan, simple gate rules |
At the end of 30 days, you won't have "perfect" DevSecOps, but you will have a working foundation on which to build maturity.

Common mistakes that cause DevSecOps to fail
The most common pitfalls seen in the field:
Security "sits on" the process, and developers circumvent it.
Too many devices too quickly, no owner, no triage.
The pipeline will be too slow, and they will start blocking checks.
There is no difference between dev and prod permissions.
There is no decision on what constitutes a "stop ship," so everything becomes a matter of debate.
If this sounds familiar, the quickest way forward is usually a short audit and a realistic roadmap. IT consulting can typically be a big help here, for example in clarifying focus and priorities: IT consulting: when is it needed and what do you get for it?
Frequently Asked Questions (FAQ)
What is the most important first DevSecOps step if I have limited time? Generally, branch protection (mandatory review) and secrets scan provide the greatest immediate risk reduction with minimal effort.
Is an SBOM necessary even if the company is not an enterprise? In many cases, yes, because it is increasingly requested due to vulnerability management and supplier issues. There is no need to overcomplicate things; a release-linked, stored SBOM is sufficient.
How much control can be applied without slowing down development? Good practice is to run only quick checks at the PR level, with more "heavy" scans performed in CI or nightly mode. Critical issues should be blocked, while the rest should be triaged and tied to SLAs.
What is the difference between DevOps and DevSecOps at the pipeline level? DevOps focuses on fast and stable delivery. DevSecOps adds automated security checks, stricter permissions, artifact authentication, and auditability.
How does cloud and cloud security relate to this? If deployment goes to the cloud, CI/CD directly modifies infrastructure (IAM, network, storage). In this case, IaC scan and policy-as-code are extremely important, otherwise the pipeline can very quickly "spread" bad configurations.
Next step: DevSecOps audit and secure CI/CD roadmap
If you want a CI/CD that is both fast and auditable, it is worth starting with a short assessment: clarifying permissions, secrets management, artifact processes, and realistic "stop ship" rules.
In addition to digitalization and IT solutions, the Syneo team can also provide support in the areas of DevOps, operations, and consulting to help you develop a stable and secure delivery process. For further context, you may find the following articles useful: DevOps basics: the path from zero to a live environment in 2026, and IT consulting: when is it needed and what do you get for it?

