Online age verification: GDPR-compliant solutions
Other
Online Age Verification: GDPR-Compliant Solutions | Syneo
How to verify age online in a GDPR-compliant manner? Data minimization methods, token-based and eID solutions, legal bases, vendor selection, and a rapid implementation plan.
age verification, GDPR, data minimization, eID, token model, KYC, data protection, DPIA, biometrics, vendor selection, auditability
March 17, 2026
In the online space, the sale or access to age-restricted products and content (such as alcohol, 18+ digital content, gambling, and certain social media features) increasingly faces the same dilemma: how do you verify age without collecting unnecessary personal data, while remaining fully GDPR-compliant?
A good solution isn’t just about legal compliance. It also makes sense from a business perspective: it reduces risk, minimizes abuse, builds trust, and helps avoid overly strict processes that hinder conversions.
(Important: This article is for informational purposes only and does not constitute legal advice. For specific industry obligations and risk levels, it is advisable to consult a data protection expert.)
What does “age verification” mean online, and what doesn’t it mean?
In practice, three different approaches are often conflated, even though they are not the same from the perspective of the GDPR and IT architecture:
Age gate (self-declaration): A gate that asks, “Are you over 18?” Minimal data, minimal verification.
Age verification: You make a decision based on a more reliable form of identification (such as eID, bank verification, document verification, or service provider verification).
Age estimation: typically involves biometric or behavior-based estimation (such as based on a facial image). It may be convenient, but it poses significant privacy risks and can easily lead to “over-collection.”
Most companies don’t actually need a “date of birth”; all they need for a business decision is a statement:
“User 18+” (yes/no)
perhaps "user 16+" or some other age restriction
If you keep this in mind, it will be much easier to build a data-minimizing, GDPR-compliant solution.
GDPR Fundamentals for Age Verification: Compliance Starts with Design
Age verification typically involves the processing of personal data (even if you simply mark a user’s account as “18+”). Document-based verification, biometrics, or third-party identity verification services further increase the risk.
It is advisable to familiarize yourself with the text of the GDPR firsthand, particularly the general principles and the sections concerning children (Articles 5, 6, and 8 of the GDPR): EUR-Lex: GDPR (2016/679).
The most important principle: data minimization and purpose limitation
The purpose of age verification is usually to prevent users under the age limit from accessing a feature or transaction. It follows that:
Don't ask for a date of birth if an "18+" designation is sufficient.
Do not save the document image if a verification result and audit trail are sufficient.
Don’t build a “one-size-fits-all” KYC process if all you need is age verification.
Legal basis: “consent” should not be given reflexively
Many implementations go wrong because they base everything on "consent." When verifying age, a more realistic legal basis is often:
to comply with a legal obligation, if your service is required by industry regulations to implement age verification,
It is a legitimate interest if the goal is to reduce risk and protect minors, and you can substantiate this through a balancing of interests.
The appropriate legal basis depends on the specific use case and legal environment; therefore, best practice here is to design your system with data protection documentation in mind, rather than simply “tacking on” the GDPR afterward.
Privacy by Design and DPIA
If your solution involves higher risks (such as document verification, biometrics, or a large number of users), a data protection impact assessment (DPIA) is typically required. The EDPB has issued specific guidance on the principles of “data protection by design and by default”: EDPB Guidelines 4/2019 on Article 25.
The table below will help you translate the principles of the GDPR into specific technical decisions.
GDPR principle | What does "age verification" mean? | Example of a "good" solution |
Data minimization | Don't collect more than what is necessary for the age-based decision | "18+ verified" label, without a date of birth |
Purpose-driven | Do not use verification data for marketing or profiling purposes | The audit result is used solely for access control purposes |
Limited shelf life | Do not keep the document unless there is a compelling reason to do so | Time-limited "age token" with automatic expiration |
Integrity and confidentiality | Robust access and logging controls | RBAC, MFA, audit log, encryption |
Accountability | Be able to explain how you made your decision and why | DPIA, balancing of interests, data flow diagram, DPA |
GDPR-compliant solutions: which one is best for what?
There is no one-size-fits-all solution. The right choice depends on the potential harm if a minor were to gain access, and the extent to which you need to prevent this in a way that can be audited.
The comparison below is not a "final verdict," but rather a perspective to aid in decision-making.
Solution | Evidentiary value | Typical data protection workload | When is it realistic? |
Self-report (age gate) | Low | Low | Low-risk content, a "courtesy" gateway |
Account + Payment Method Verification | Medium | Medium | Subscription models where payment is required anyway |
Third-party age verification provider (token-based) | Medium-high | Medium | If you need a scalable, auditable solution and don't want to deal with paperwork |
eID-based authentication (where available) | High | Medium | Stronger compliance, higher risk, regulated sector |
Document scan + selfie/biometrics | High (but not flawless) | High | In cases involving particularly high risk and a high standard of proof |
The "token-based" model is your best friend when it comes to data minimization
If the service provider can return the result in such a way that this is all you receive:
age_over_18 = trueverified_at = timestampverification_id = reference(for audit purposes)
then you can avoid generating large amounts of sensitive identification data within your own system.
Decision-making framework: What “age limit coverage level” do you need?
It is worth introducing a risk-based scale and aligning technology, UX, and data management with it.
Level | The risk of being wrong | Sample recommended solution | A typical UX effect |
Basic | Low reputational risk | Age gate + server-side enforcement | Minimal friction |
Medium | Financial and compliance risk | Token-based third-party verification with re-verification rules | Medium friction |
High | Serious legal consequences, auditability requirements | Strong authentication (eID), strict logging, DPIA, vendor audit | Higher friction |
The most common mistake is that teams choose the "high" level for everything, and then the solution:
it will be expensive,
reduces conversion rates,
it will also pose a greater risk from a data protection perspective (because it involves the transfer of more data).
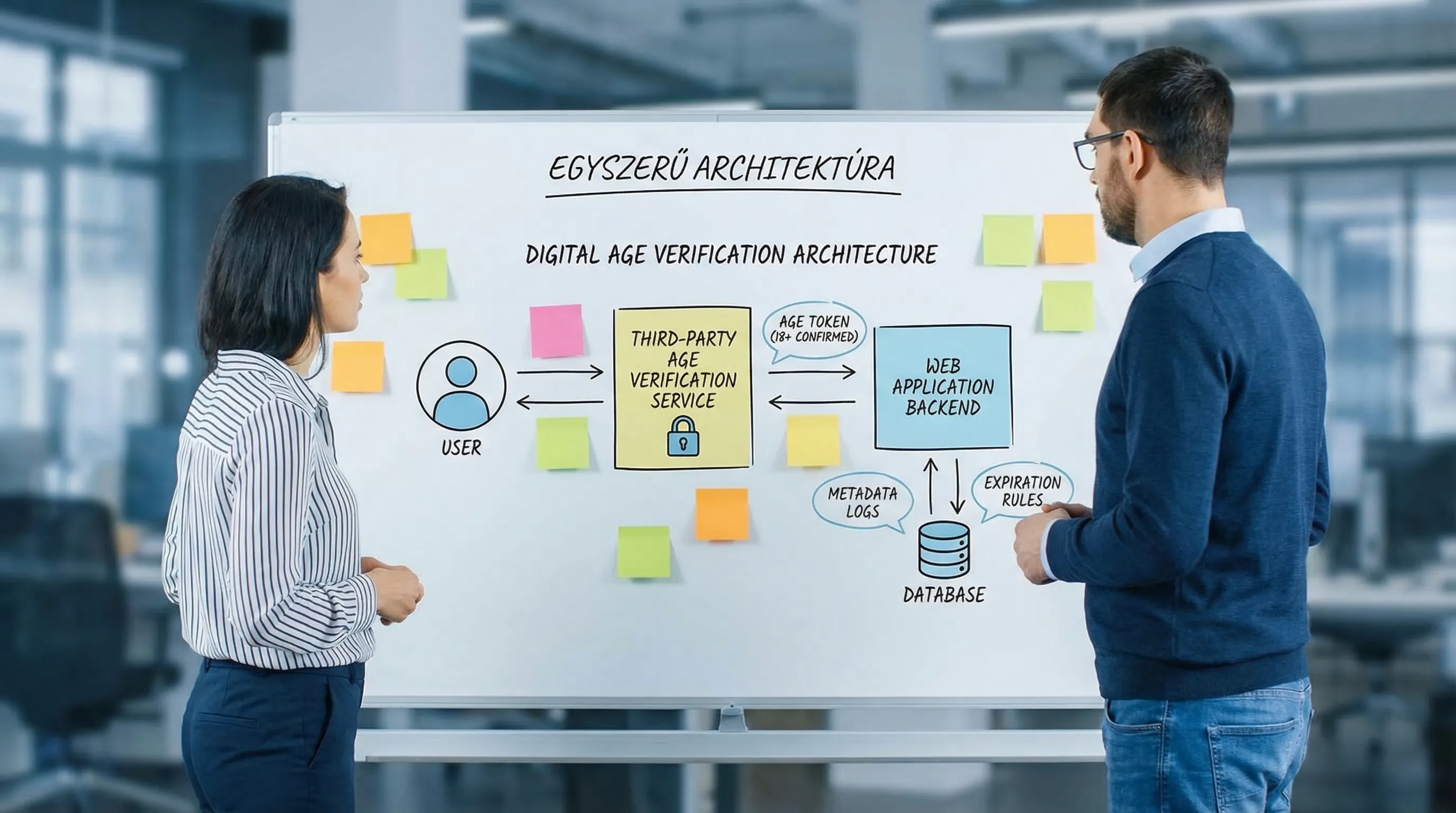
Recommended architecture: "age assertion" instead of storing documents
One best practice for GDPR-compliant age verification is to separate:
the service provider conducting the inspection,
access control for your system,
and an auditable audit trail.
Technical "basics" that many people overlook
Server-side enforcement: the front-end age gate alone is not enough; the backend must also be able to block age-restricted operations.
Session and token management: include a TTL, renewal logic, and protection against replay attacks.
Audit log: when the check was performed, what threshold was used, what method was employed, and what decision was made.
Access management: verification status and logs should not be accessible to "all admins."
If you want to streamline access management and logging at the system level, the logic behind authentication and security minimums is very similar (RBAC, MFA, session rules): E-invoice login: access management and security minimums.
Choosing a supplier and drafting a contract: this is where half of the GDPR risk is determined
Age verification is typically provided by a third-party vendor (SaaS or an integrated service). In this case, you are not just choosing a technology, but also a data management model.
Determine the roles: data controller, data processor, joint data controllers
It matters who the service provider is:
acts in accordance with your instructions (data processor),
or uses data for its own purposes (which may already constitute the role of a data controller).
This must be clarified in the contract and adjusted accordingly:
the brochure,
the legal basis,
and the user experience.
A Supplier Checklist That Really Matters
Data-minimizing response: Can you verify that someone is "18+" without sharing any document data?
Retention and deletion policy: How long do you retain data, and what is the deletion SLA?
EU/EEA data residency and data transfers: Where is the service hosted, are there any transfers outside the EEA, and what is the legal framework?
Logging and access: Who has access to verification data at the service provider, and are there robust controls in place?
Incident management: reporting deadlines, cooperation, forensic logs.
Without basic cybersecurity controls, GDPR compliance is also at risk. If you need a quick baseline, it’s worth starting with the minimum controls (MFA, backups, logging, incident response): Cybersecurity for SMEs: 10 Minimum Controls by 2026.
Common Design Mistakes (and What to Do Instead)
“Just enter your date of birth, and you’re done”
A date of birth is more than is necessary, and in many cases, it can easily be forged. Instead:
use age-restricted content (18+),
and, if necessary, back it up with external verification.
Storing ID photos just to be on the safe side
This typically conflicts with data minimization and poses a serious data security risk. Instead:
auditable reference,
short-lived token,
strict retention (and verifiable deletion).
Front-end control only
If the backend APIs are not secured, the age gate can be bypassed. Instead:
policy in the backend,
authorization model (for example
age_verified=true(based on the claim),and marked decision points.
There is no re-inspection rule
An 18+ rating isn't necessarily permanent. Instead:
define a maturity (for example, based on risk),
and manage the risks associated with account sharing.
Rapid implementation plan: Live and auditable in 2–4 weeks
The timeline depends on which systems need to be integrated (online store, CRM, IAM, payment processing, customer service), but a low-risk MVP is often ready sooner than you might think.
Week 1: Scope and Risk Level
specify the age threshold and the prohibited actions,
Create a data flow diagram (showing where everything goes),
Decide on the desired "level of coverage."
Week 2: Suppliers and Architecture
Choose a token-based or eID-based model,
document the retention and audit requirements,
Launch a PoC on the critical user path.
Weeks 3–4: Integration, logging, deployment
backend enforcement,
logging and monitoring,
information and processes (support, incident, deletion),
Go-live, followed by a short hypercare period.
When multiple systems are involved, the quality of the integration is key. It’s a good idea to establish an integration map and define responsibilities right from the start: System Integration: How to Connect ERP, CRM, and BI?
How can Syneo help with this?
GDPR-compliant age verification is not simply a matter of a single “plugin,” but rather a combination of processes, architecture, vendor compliance, and security controls.
Syneo can help ensure that the solution not only works, but is also auditable and commercially viable:
determining requirements and risk levels (what needs to be demonstrated and to what extent),
architecture and integration plan (age token, IAM, logging, retention),
supplier evaluation (DPA, data flow, security minimums),
implementation support (custom development, DevOps, operations).
To move forward, it’s a good idea to start with a brief, targeted assessment that, over the course of 1–2 workshops, clarifies the necessary security requirements, data flows, and the fastest path to an MVP. For more information: Syneo.

