Talend DevOps: CI/CD Pipeline Template and Release Best Practices
Other
Talend DevOps: CI/CD Pipeline Template and Release Best Practices | Syneo
A Practical Guide to Implementing Talend DevOps: Sample CI/CD pipeline, environment management, release best practices, and a 30-day starter plan for mitigating risks.
Talend, DevOps, CI/CD, pipeline, release, release management, DevSecOps, observability, data streams, artifact repository, Talend jobs, Syneo
April 4, 2026
For many teams, Talend is “critical infrastructure”: it powers ERP, CRM, BI, and data reporting integrations, yet it is often kept alive by manual exports, ad hoc hotfixes, and “overnight fixes.” In such cases, the focus is not on product development, but on risk management. The goal of Talend DevOps is to make data flow delivery just as disciplined, automated, and auditable as that of a modern application: versioning, CI/CD, testing, environment promotion, and rollback plans.
This article provides a CI/CD pipeline template and release best practices for Talend-based solutions, with a particular focus on practical feasibility (and where things tend to go wrong).
What do we mean by Talend DevOps (and why not just “build automation”)
In a Talend environment, DevOps typically isn’t just about a single deployment step, but rather the collaboration of multiple components:
Versioning of Talend jobs and components (code + metadata + configuration templates).
Automation of builds and packaging (typically using Maven-based builds or Talend CLI/CI tools, depending on the version of Talend used).
Managing environment-specific configurations (connections, endpoints, resources, schedules, permissions).
Automated testing and quality gates (code quality, dependency risk, data validation).
Controlled release and promotion (dev → test → stage → prod), with audit trails.
Operationality: logging, observability, alerts, incident management.
Most Talend projects start to run into trouble when they have only one or two of the above elements in place, while the rest rely on manual "heroic efforts." The CI/CD pipeline template shows exactly how to build a stable system.
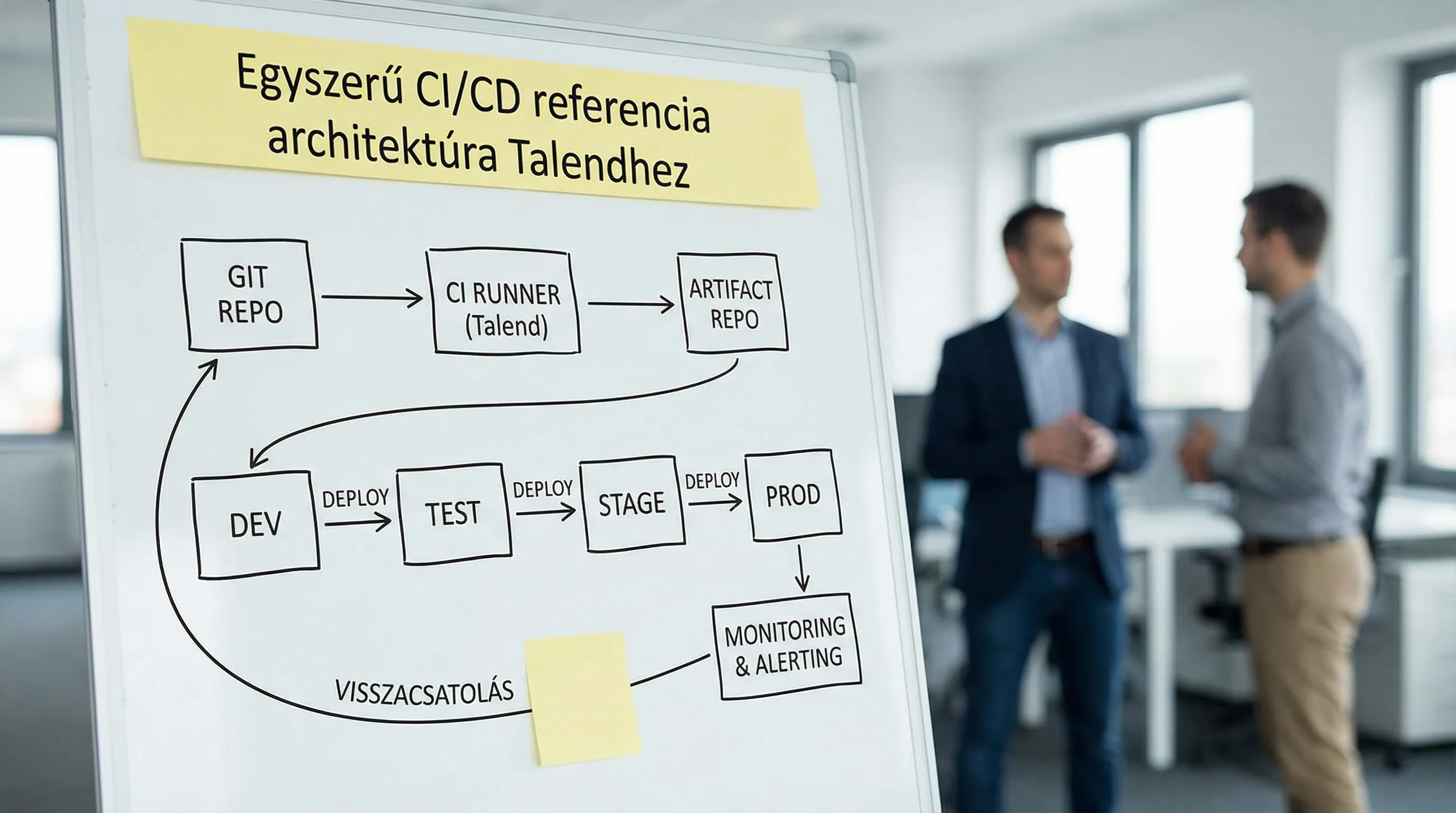
Reference architecture: repo, build runner, artifact repository, runtime environment
In the most effective Talend DevOps setups, the pipeline isn’t a “Talend-specific snowflake” but aligns with the company’s delivery standards (Azure DevOps, GitLab CI, GitHub Actions, Jenkins, etc.). Talend handles what and how you build, as well as how you configure it.
The following table shows a practical, vendor-neutral base model:
Building component | What does he do? | A Talend feature to keep in mind |
Git repository | Code, configuration templates, pipeline definition | Jobs, shared context, SQL statements, and mappings are versioned together in a unified structure |
CI runner | Build, test, quality gates | The build should be reproducible and "headless," not a manual export from Studio |
Artifact repository | Storing versioned build output | Not a "zip file via email," but a traceable build artifact |
CD orchestrator | Deployment/promotion environments | Configuration and secrets should not be included in the artifact |
Runtime (JobServer/Cloud Runner) | Deployment and scaling | Permissions, network, connectivity, resource limits |
Observability | Logos, metrics, alerts | Job run statuses, throughput, error classification, SLAs |
It’s a good idea to use team standards for branch and PR rules. If you use Azure DevOps, the guide on branch strategies and PR rules for teams is a useful supplement to your internal guidelines.
Sample CI/CD pipeline for Talend: minimal viable, yet scalable
The goal of the pipeline is to ensure that every change results in a reproducible build, with automated checks, and that only "green" packages proceed to release.
CI (build) stages: recommended steps
The table below shows a typical CI pipeline structure. The specific commands depend on the Talend version and the build method, but the logic remains consistent.
Stage | What to check | What does it output? |
Checkout + Versioning | Tag/commit identification, version number generation | Build metadata (commit hash, branch, build number) |
Build (headless) | Translation, packaging | Versioned artifact (e.g., job package) |
Structural inspections | Lint, basic code quality, "prohibited patterns" | Report, quality gate |
Dependency/Component Risk | Vulnerabilities in dependencies, licensing risks | SCA Report, Gate Rules |
Tests | Unit, integration, and smoke test runs | Test report, coverage where applicable |
Publishing Artifacts | Uploading an artifact to the repository | Searchable, downloadable package |
At Talend, it is particularly important that the build:
does not require a developer machine or the Studio GUI,
be deterministic (the same output from the same commit),
and include build evidence (logs, version, test reports).
When it comes to DevSecOps gateways (secrets, SAST/SCA, SBOM, signing), it’s a good idea to follow a consistent company-wide template. The article “DevSecOps in Practice: How to Build Secure CI/CD” provides a solid foundation for this.
Example: Logic of a pipeline definition (device-independent pseudo-code)
The following section is not tied to any specific platform; the key points are the order of the stages and the gates:
If you stick to this minimum, you can later build on it in a controlled manner (data validation, contract tests, performance checks).
CD and environmental promotion: don’t “deploy,” but “promote”
With Talend systems, the greatest operational risk arises when the same job behaves differently across environments, and the difference is not apparent from the code. For this reason, the key to continuous deployment is not rapid deployment, but disciplined environment management.
Environment model: dev, test, stage, prod
Recommended approach: Run the same artifact across all environments, changing only the configuration.
Environment | Goal | Typical control |
Dev | rapid iteration | A more lenient gate, but a CI build is required |
Body | integration and regression | automated test data, stable dependencies |
Stage (pre-production) | near-live test | release candidate, production configuration "mirror" |
Prod | Business SLA | approval, change record, monitoring, rollback plan |
Configuration best practices: Separating context and secrets
Talend’s “context”-based parameterization is a good foundation, but it typically goes awry when the team takes the easy way out and “hard-codes” environment values. Recommended minimums for release:
Configuration templates in the repository: only the keys and structure, not the actual values.
Special handling of secrets: vault, secret store, or at least pipeline secret variables.
Configuration drift control: Differences between stage and production environments must be traceable (change log, diff, audit).
Integration environments involve a particularly large number of dependencies (ERP/CRM APIs, databases, SFTP, message queues). If the integration map isn’t in order, the CD is “just a CD on paper.” Related background: System integration: how do you connect ERP, CRM, and BI?
Release Best Practices for Talend: Versioning, Packaging, Approval, Rollback
Talend release management works well when a "release" isn't just a single point in time, but a repeatable process where you know in advance:
who's going out,
what has changed,
How do you prove that it's good?
and what happens if it's wrong.
Versioning and answering the question "What's live?"
The minimum goal: to be able to say about any live run:
which Git commit it was built from,
which version of Artifact is running,
which configuration version,
and who approved it.
Practical example:
Git tag for a release (e.g.,
v1.8.0or2026.04.1).The Artifact version matches the tag.
Automatic generation of release notes from PR tags and ticket links.
The branching model can be GitFlow-style or trunk-based; the key is consistency. In a trunk-based model, robust CI and a risk-mitigating deployment pattern—such as feature flags—are particularly important.
Release checklist: ETL/ELT-specific items
Compared to application releases, data streams involve different types of risks (data duplication, partial processing, and corruption of downstream reports). The table below outlines the core elements of a Talend release checklist:
Area | Inspection | Typical evidence |
Data model change | schema, mapping, types, null handling | diff, migration ticket, test report |
Idempotence | rerun without duplication | test run evidence, control boards |
Error Handling | retry, dead-letter, alert | log sample, alarm test |
Performance | runtime, resource peaks | baseline vs. new measurement |
Scroll back | Quickly restore a previous version | rollback runbook, artifact availability |
Operation | dashboard, alert rules, on-call | monitor configuration, ownership (RACI) |
"Idempotence" is particularly important: if a sharp right turn fails halfway through, or if the system attempts it twice, the data loss could be much more costly than the error itself.
Quality Gates: What to Automate in Talend Pipelines
CI/CD delivers real speed only when it is not just fast, but also reliable. To achieve this, quality must be built into the pipeline.
Test levels: what to run and where
Test type | What is it good for? | Where to run |
Build smoke | foldable, packable | all PR |
Component-level verification | the logic of critical transformations | After the PR and main merge |
Integration test | external systems, databases, APIs | nightly or merge gate |
Data validation | field level, range, keys, duplication | in a production/staging environment |
Regression | previous mistakes shouldn't happen again | before the release candidate |
Many teams use explicit rule sets or dedicated data quality frameworks for data validation. The goal is not to “test everything,” but rather to ensure that:
a few business-critical safeguards (e.g., number of records, uniqueness of keys, required fields, balance verification),
and set up an alert in case it gets damaged.
Observability and SLAs: Talend DevOps determines what you see in production
The first question after a release isn’t whether it “went live,” but whether it works on a business level. This requires observability.
Recommended minimum metrics for Talend job runs:
Running time (average, percentiles, trend)
Number of processed records (input, output, reject)
Error rate and error category (connection error, data quality error, timeout)
Number of retries, retry events
Downstream SLA metrics (e.g., BI refresh time)
When measuring delivery performance, it’s a good idea to start with DORA-style metrics. The Google Cloud DORA resources hub provides a good overview of the basics of DORA.
Once your team has completed the assessment, the next step is to map out your DevOps maturity. Related resource: DevOps Maturity Assessment: Where Does Your Team Stand?
Talend DevSecOps: The Most Common Security Vulnerabilities and the Minimum Required Fixes
Talend integrations typically have "access to everything": databases, file systems, APIs, and sometimes even personal data. As a result, without DevOps, not only does the risk to system stability increase, but so does the risk to information security.
Common mistakes:
Passwords are included in the repository or export package.
Service accounts are granted too broad permissions.
The pipeline runner has too much access to the environments.
It's not clear who deployed what and when.
Recommended minimum checks:
Secrets only from the secret storage, on a rotating basis.
Least privilege for the running user and connections.
Separation of build and deployment (separate identity, separate scope).
Artifact integrity: Deploy from a verified source.
If an organization is subject to regulatory pressure (e.g., NIS2), CI/CD evidence and access management are typically audit points. Basics: Cybersecurity for SMEs: 10 minimum controls by 2026
Common "anti-patterns" in Talend releases (and how to fix them)
The following patterns almost always slow down delivery and increase the error rate:
Manual export and manual upload: cannot be reproduced or audited.
Environment-specific job forks: the same logic in multiple places—guaranteed drift.
There is no intermediate stage: a rehearsal environment that closely resembles a live performance is needed between the rehearsal and the production.
Release notes "off the top of my head": no clear list of changes, wasted time debugging.
The solution to these issues is generally not “more documentation,” but rather a pipeline and governance. Project management in IT is closely tied to the practical aspects of governance : this is what makes the delivery schedule predictable.
30-Day Starter Plan: Low-Risk Talend CI/CD Implementation
In most organizations, the best approach is a controlled pilot, not an “all-at-once” transition.
Week 1: Baseline and Scope
Select 1–3 business-critical jobs and describe them:
where is the source code,
how the build is created today,
where it runs and how it is scheduled,
What kind of SLA does the business expect?
what caused the last three serious incidents.
Week 2: Reproducible Build and Artifact
The goal is to have:
a headless build process,
versioned artifact,
and at least one automatic smoke test for PR.
Week 3: Environmental Management and Promotion
Sort by:
configuration templates (repo),
secrets (secret storage),
and set up a stage-like environment or a sharp mirror, if you haven't already.
Week 4: Release runbook + monitoring
Make sure you have the minimum operating package:
release checklist and approval points,
rollback steps,
Basic alerts and a dashboard for job runs.
If you want to organize this in a structured way, it’s a good idea to treat the work as a measurable backlog. A good framework for this is: DevOps work items: how to build a well-measurable backlog
How can Syneo help with this?
A Talend DevOps implementation typically progresses quickly when the team focuses not on tools, but on delivery capabilities: how quickly and with what level of risk you can deploy changes to production.
At Syneo, we can help with this by tailoring our solutions to your existing environment:
CI/CD pipeline design and implementation (build, artifact, deployment model)
Establishing DevSecOps gateways and auditable evidence
Release process and runbooks, rollback and hypercare operations
Measurement and stabilization (DORA-style metrics, reducing incident causes)
If you have specific Talend-based integration workloads (ERP, CRM, BI, data reporting) and your current processes are too manual or risky, it’s worth starting with a brief, targeted assessment, after which we can provide a detailed implementation plan tailored to your toolchain.

